Give Your AI Assistant a Longer Reach: Setting Up Tailscale with FileSurf
How to connect your FileSurf AI container to your personal devices using Tailscale — giving your assistant secure SSH access to your home server, Raspberry Pi, or any machine on your tailnet.
2026-03-08
What is Tailscale?
Tailscale is a mesh VPN that connects your devices securely over the internet. Think of it as a private, encrypted network that spans all your devices—no matter where they are in the world.
Why Tailscale?
| Traditional VPN | Tailscale |
|---|---|
| Centralized server required | Peer-to-peer mesh |
| Complex server setup | Automatic key exchange |
| Single point of failure | No single point of failure |
| Hard to scale | Grows with your devices |
Tailscale creates a private tailnet—a network where every device can directly communicate with every other device, using end-to-end encryption. It's like having a direct, secure tunnel from your FileSurf session to your home computer, without exposing anything to the public internet.
It Works Everywhere
One of Tailscale's superpowers is its cross-platform support:
- macOS - Native app
- Windows - Native app
- Linux - Install via package manager or userspace binary
- iOS/Android - Mobile apps
- Raspberry Pi - Works perfectly
- Home routers - Many support Tailscale natively
Setting Up Tailscale with FileSurf
Here's how to give your FileSurf AI tentacles to reach your other devices.
Step 1: Get Your Auth Key from Tailscale
Head to the Tailscale admin console and generate an auth key:
- Go to login.tailscale.com/admin/settings/keys
- Click Generate auth key
- Choose whether it should be reusable and set an expiry
- Copy the key — it looks like
tskey-auth-...
Note: This key grants permission to add your FileSurf container to your tailnet. Keep it safe — don't paste it into chat logs or share it publicly.
Step 2: Save Your Auth Key in FileSurf
FileSurf expects your Tailscale auth key at a specific location in your workspace:
echo 'tskey-auth-YOUR-KEY-HERE' > /workspace/.tailscale-auth-token
chmod 600 /workspace/.tailscale-auth-tokenThis file is read automatically by the Tailscale daemon on startup. The key is only used on the first connection — after that, Tailscale persists its state so it reconnects automatically on subsequent restarts without needing the key again.
Step 3: Ask FileSurf to Set Up the Tailscale Daemon
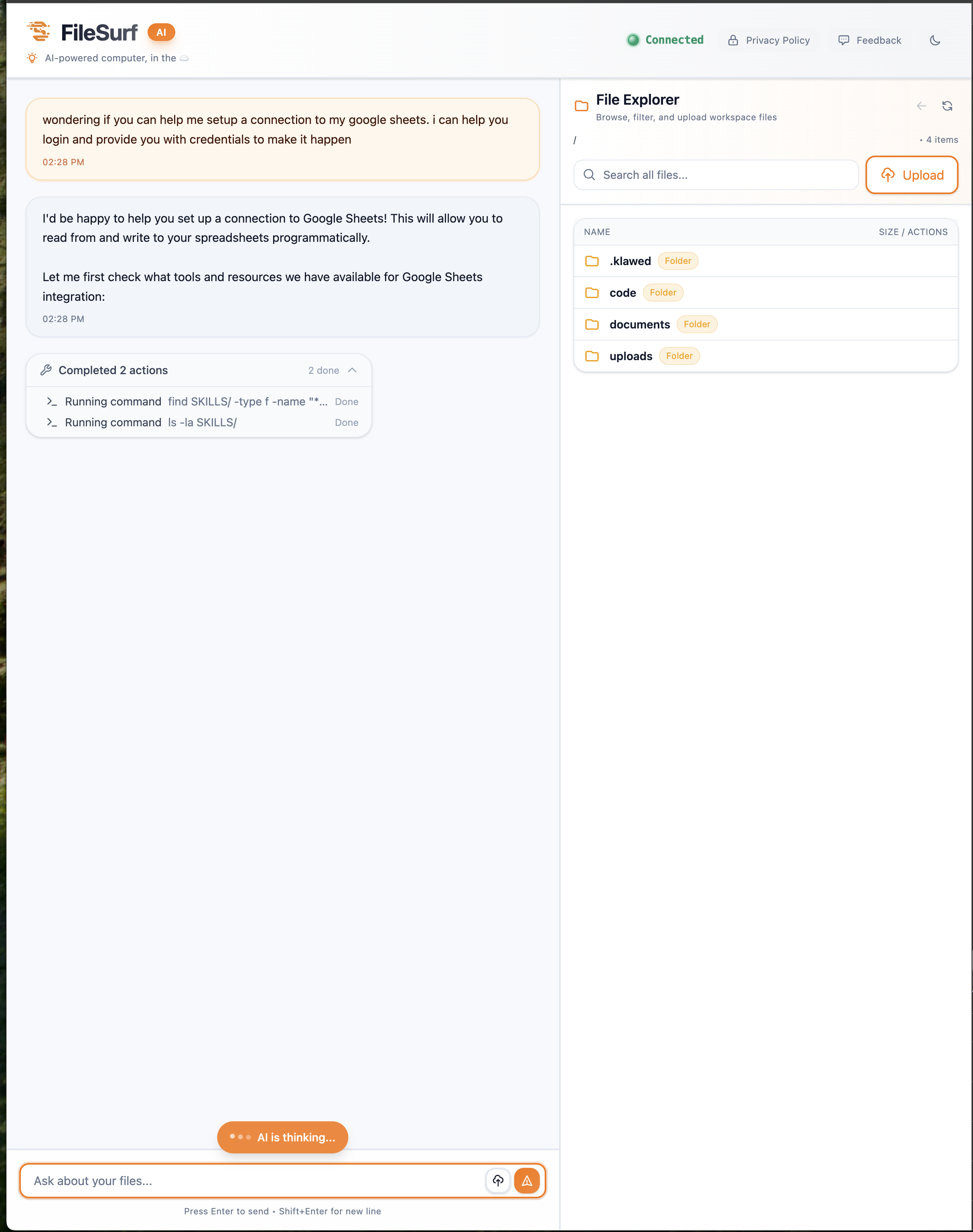
FileSurf's AI can write and configure the Tailscale background service for you. Just paste this prompt into the chat:
Please set up a Tailscale daemon for me. It should:
- Run
tailscaledin userspace networking mode (no kernel TUN required)- Store state and the socket in
/workspace/run/tailscale/- Use the Tailscale binaries at
/workspace/bin/tailscaledand/workspace/bin/tailscale- Read the auth key from
/workspace/.tailscale-auth-tokenif it exists, and runtailscale up --authkey=... --accept-routes --resetto connect- Only attempt to authenticate if the token file is present — if it's missing, the daemon should still start (state may already exist from a previous run)
- Run
tailscaledin the foreground as the main process so the supervisor can monitor and restart it directly- The auth step should happen in a background subshell so it doesn't block the daemon from starting
FileSurf will write the daemon script and register it as a background service that starts automatically with your container and restarts if it ever crashes.
Step 4: Connect SSH to Your Other Devices
Now that Tailscale is running in your FileSurf container, configure your target devices to accept SSH connections from it.
Generate an SSH Key
FileSurf can generate an SSH key for you. Just ask:
Generate an SSH key for meFileSurf will create one at /workspace/.ssh/id_ed25519 (public key at /workspace/.ssh/id_ed25519.pub).
Add Your Public Key to Target Hosts
Copy your public key and add it to the authorized_keys file on each device you want FileSurf to access:
# On your target device (e.g., home server, Raspberry Pi)
mkdir -p ~/.ssh
chmod 700 ~/.ssh
echo "ssh-ed25519 AAAA... your-public-key-here..." >> ~/.ssh/authorized_keys
chmod 600 ~/.ssh/authorized_keysOnce that's done, you can SSH directly from your FileSurf session to that device using its Tailscale hostname (e.g., raspberrypi or home-server).
What's Possible Now?
With Tailscale connected, your FileSurf AI can:
- Access your home files - "Check my photos directory on the home server"
- Control IoT devices - "Turn on the lights via my Raspberry Pi"
- Manage cloud resources - "SSH into my EC2 instance and check the logs"
- Deploy code - "Push this update to my personal server"
- Monitor systems - "Check the health of my home lab"
The AI isn't just trapped in the container anymore—it can reach out and touch the rest of your digital infrastructure.
Summary
- Get a Tailscale auth key from login.tailscale.com/admin/settings/keys
- Save it to
/workspace/.tailscale-auth-tokenwithchmod 600 - Ask FileSurf to set up the Tailscale daemon using the prompt above
- Generate an SSH key via FileSurf and add it to your devices'
authorized_keys - Your AI now has tentacles to reach your entire digital ecosystem
The future of useful AI isn't just about smarter models—it's about giving AI the ability to reach beyond its container and connect to the edges of our digital lives.
Happy networking! 🚀